Sniper Africa Fundamentals Explained
Sniper Africa Fundamentals Explained
Blog Article
Sniper Africa Things To Know Before You Buy
Table of ContentsSome Ideas on Sniper Africa You Need To KnowGetting My Sniper Africa To WorkThe Ultimate Guide To Sniper AfricaThe Main Principles Of Sniper Africa Sniper Africa Things To Know Before You BuyExamine This Report about Sniper AfricaSome Known Details About Sniper Africa

This can be a specific system, a network area, or a theory caused by an announced susceptability or patch, details concerning a zero-day exploit, an abnormality within the security data collection, or a demand from elsewhere in the organization. As soon as a trigger is determined, the hunting initiatives are concentrated on proactively looking for abnormalities that either confirm or refute the hypothesis.
Top Guidelines Of Sniper Africa

This process may include making use of automated devices and inquiries, in addition to manual evaluation and relationship of data. Unstructured searching, likewise called exploratory searching, is a much more open-ended approach to danger searching that does not depend on predefined standards or theories. Instead, risk hunters use their knowledge and instinct to browse for possible threats or vulnerabilities within an organization's network or systems, frequently concentrating on locations that are viewed as high-risk or have a background of protection occurrences.
In this situational technique, threat hunters make use of hazard intelligence, in addition to other pertinent data and contextual info about the entities on the network, to determine possible dangers or susceptabilities related to the scenario. This might involve using both structured and unstructured hunting methods, as well as collaboration with various other stakeholders within the company, such as IT, legal, or business groups.
Sniper Africa Can Be Fun For Anyone
(https://pxhere.com/en/photographer/4556048)You can input and search on hazard knowledge such as IoCs, IP addresses, hash worths, and domain name names. This process can be integrated with your security info and occasion management (SIEM) and risk intelligence tools, which use the intelligence to hunt for threats. Another great resource of knowledge is the host or network artifacts given by computer system emergency response groups (CERTs) or details sharing and evaluation facilities (ISAC), which might allow you to export automated signals or share key info regarding new assaults seen in other companies.
The very first step is to recognize APT groups and malware strikes by leveraging global discovery playbooks. This strategy frequently lines up with threat structures such as the MITRE ATT&CKTM structure. Below are the activities that are most frequently involved in the process: Use IoAs and TTPs to identify danger stars. The hunter analyzes the domain, setting, and assault actions to produce a theory that lines up with ATT&CK.
The objective is locating, determining, and after that isolating the hazard to prevent spread or expansion. The crossbreed threat searching strategy integrates all of the above approaches, permitting safety and security analysts to personalize the hunt.
The 7-Minute Rule for Sniper Africa
When working in a protection procedures center (SOC), hazard seekers report to the SOC manager. Some important abilities for a great hazard seeker are: It is crucial for threat seekers to be able to interact both vocally and in composing with excellent clearness about their tasks, from examination all the method via to searchings for and recommendations for remediation.
Data violations and cyberattacks cost companies countless dollars every year. These tips can help your organization much better discover these dangers: Danger hunters need to sift via strange activities and recognize the actual hazards, so it is vital to recognize what the normal functional tasks of the company are. To complete this, the threat searching team collaborates with essential personnel both within and outside of IT to gather have a peek here beneficial information and insights.
The Facts About Sniper Africa Revealed
This process can be automated making use of an innovation like UEBA, which can show normal operation problems for an atmosphere, and the customers and devices within it. Hazard hunters use this strategy, borrowed from the armed forces, in cyber war. OODA stands for: Routinely accumulate logs from IT and safety and security systems. Cross-check the information versus existing info.
Determine the correct strategy according to the event condition. In case of an assault, execute the occurrence response plan. Take actions to avoid comparable attacks in the future. A threat hunting group must have enough of the following: a danger searching group that includes, at minimum, one experienced cyber risk hunter a fundamental risk searching facilities that collects and organizes protection occurrences and occasions software program made to identify anomalies and track down enemies Risk seekers utilize options and devices to find suspicious activities.
The Only Guide to Sniper Africa
Unlike automated hazard discovery systems, risk searching relies greatly on human instinct, complemented by advanced devices. The stakes are high: A successful cyberattack can lead to data violations, economic losses, and reputational damage. Threat-hunting tools supply safety groups with the understandings and abilities needed to stay one step ahead of assailants.
The Best Guide To Sniper Africa
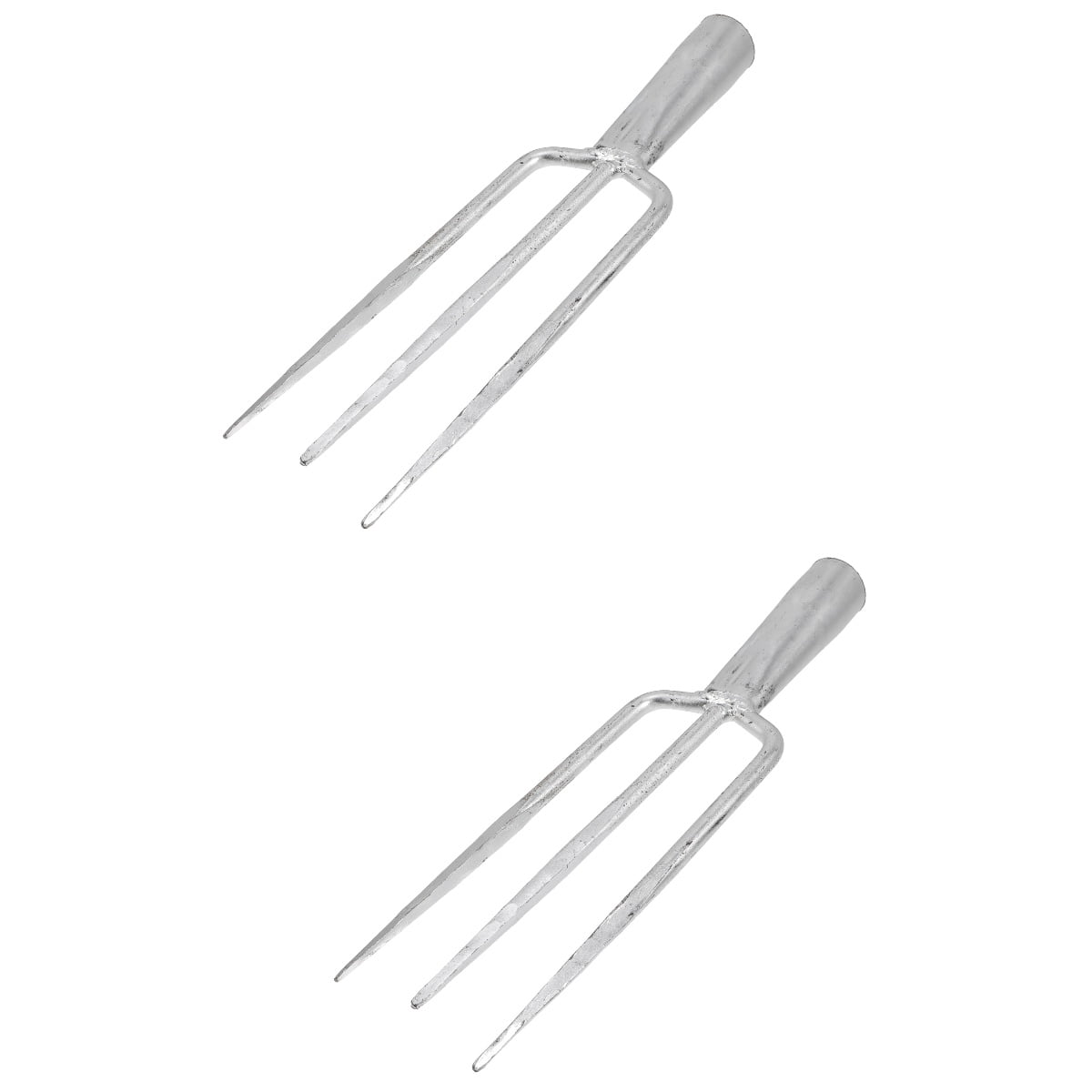
Right here are the characteristics of efficient threat-hunting tools: Continuous monitoring of network website traffic, endpoints, and logs. Seamless compatibility with existing safety facilities. hunting pants.
Report this page